TrustSec
TrustSec strengthens segmentation by tying policy to identity and role, not just IPs and subnets. Majentai maps identities to access intent, defines scalable policy groups, and creates enforceable controls that stay consistent as users move.
Why TrustSec Matters
TrustSec contains risk by limiting who and what can reach sensitive systems, and by keeping access decisions consistent across the network.
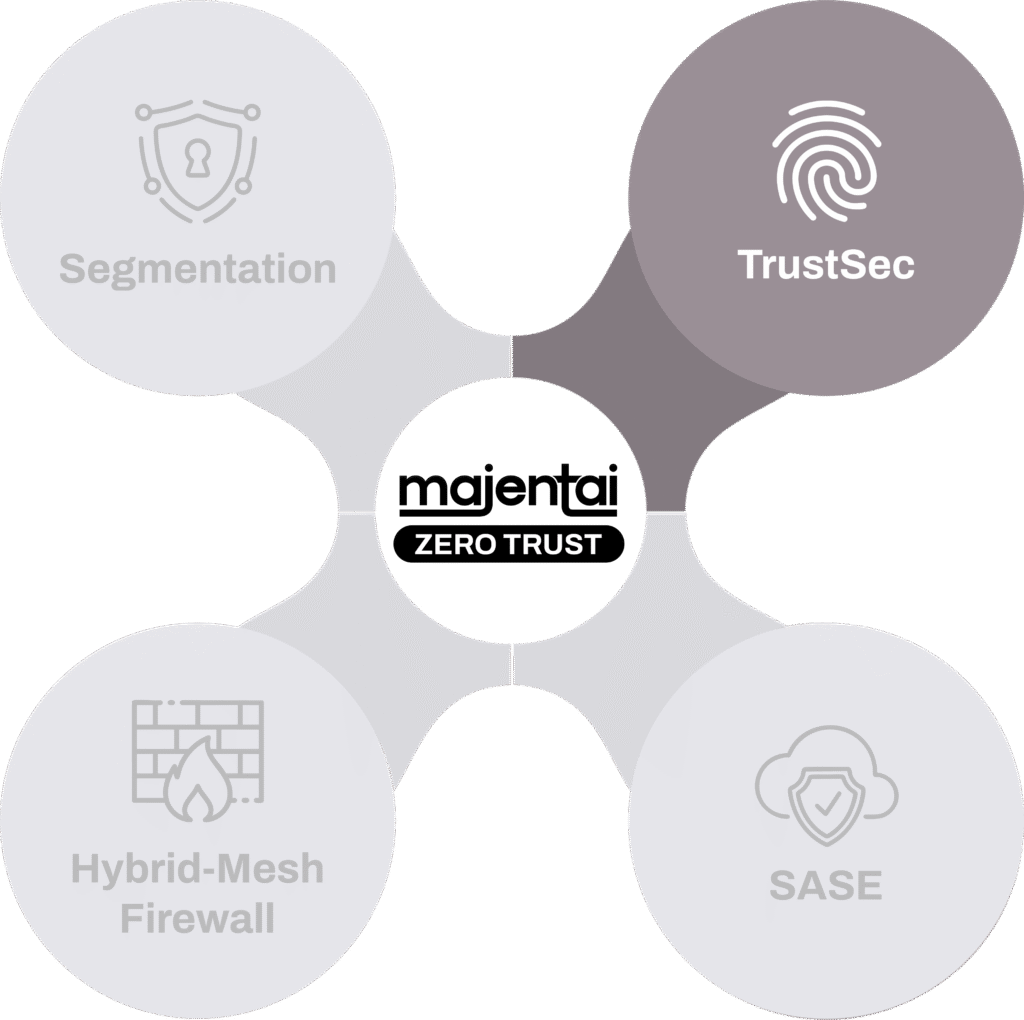
TrustSec is strongest when identity sources are clean, roles are well-defined, and policy is expressed in simple, repeatable groupings.
- Reduce lateral movement by enforcing role-based access between segments
- Protect critical systems with tighter, auditable access boundaries
- Simplify operations by replacing fragile IP rules with identity-based policy
- Enable safer third-party and contractor access with clear, limited entitlements
What We Deliver
Majentai delivers security outcomes in three connected phases that keep strategy, delivery, and operations aligned. Model clarifies the architecture, priorities, and roadmap. Adopt implements the solution, enables the team, and drives adoption from MVP through rollout. Guard sustains results with day-2 monitoring, tuning, and ongoing operational support.
Model
Discovery and design to align solutions through Workshop, Assessment, Design, and Proof of Value engagements, with clear scope, clear priorities, and a plan to execute.
Adopt
Build and deploy by delivering MVP, Implementation, and Migration engagements, enabling teams, driving adoption, and delivering progress without operational drag.
Guard
Maintain and improve posture over time with day-2 monitoring and SecOps support with Guardian Support (Managed Services), keeping controls effective as environments change.
We’re here to help.
Get clear, practical Zero Trust segmentation you can deploy with confidence.