Cisco Identity Services Engine (ISE) Solution Overview
Cisco Identity Services Engine (ISE) helps modernize network access, device visibility, and policy control across wired, wireless, VPN, guest, and segmentation services. Majentai supports the ISE lifecycle with offerings spanning workshops, assessments, PoVs, MVPs, implementations, migrations, and Guardian Support to help turn ISE into a Zero Trust and segmentation foundation.
OT Identity & Visibility

Establish trusted OT device identity and context (what the device is, where it lives, and how it behaves) before introducing Cisco ISE enforcement and TrustSec segmentation. This reduces operational risk and removes the common fear of disrupting critical OT operations that can keep organizations in monitor-only mode indefinitely.
IoT/OT Segmentation with Cisco ISE & TrustSec

Magentai helps teams reduce OT risk by applying identity-based segmentation using Cisco ISE and TrustSec. ISE identifies and classifies OT and IoT endpoints and assigns Security Group Tags (SGTs). TrustSec enforces policy between device groups to limit lateral movement, protect critical assets like historians and SCADA, and govern vendor access without creating unmanageable VLAN and ACL sprawl.
Cisco Secure Access (CSA) Solution Overview
Cisco Secure Access (CSA) helps teams modernize user and application access with a cloud-delivered architecture that supports secure internet and private application access, plus policy-based control across distributed users, devices, and environments. Majentai supports the full CSA lifecycle with offerings spanning assessments, implementations, and day-2 operational support.
Cisco Secure Workload (CSW) Solution Overview
Cisco Secure Workload (CSW) helps teams reduce risk with zero trust micro-segmentation across data center, cloud, and container environments. Majentai supports the full CSW lifecycle with a range of offerings, from workshops and assessments to PoVs, MVPs, implementations, migrations, and day-2 operational support to sustain enforcement over time.
Win Wire: Transportation
A leading transportation company engaged Majentai to modernize its firewall and core network infrastructure in preparation for long-term growth.
Win Wire: Medical Center
A medical center partnered with Majentai to replace Pulse Secure with Cisco Secure Access and complete a full production rollout. Cisco handled initial onboarding, then transitioned delivery to Majentai to deploy Secure Access and integrate related EA components including Umbrella, Duo, and ISE. The legacy VPN platform was reaching end-of-life, was capacity constrained, and had become operationally cumbersome due to certificate-based authentication and limited user support. The engagement expands a limited Secure Access pilot by improving identity integrations and shifting deployment toward network tunnels to enable private access rules, better telemetry, and VPN-as-a-service capabilities.
Win Wire: Textile Manufacturing
A global textile manufacturing company partnered with Majentai for a Segmentation Readiness Assessment and onsite workshop focused on ISE consolidation and OT network security. The engagement reviewed multiple independently managed regional ISE deployments and identified additional regions needing coverage. Majentai aligned stakeholders on a simplified future-state direction that supports centralized policy management while maintaining regional authentication needs for manufacturing sites. The team also defined a phased crawl-walk-run plan that starts with monitoring and profiling, then moves into staged enforcement as operational maturity increases.
Win Wire: Furniture Manufacturing
A large furniture manufacturing company partnered with Majentai and Cisco to deliver a Cisco ISE proof-of-value for enterprise wireless access. The engagement focused on validating 802.1X-based, identity-driven access with smooth user onboarding, dynamic policy enforcement, and stronger visibility into device posture. The work also supports a transition away from shared PSKs toward certificate-based authentication and authorization to improve control and reduce credential sharing. This PoV establishes the foundation for scaling Zero Trust access across the wireless environment.
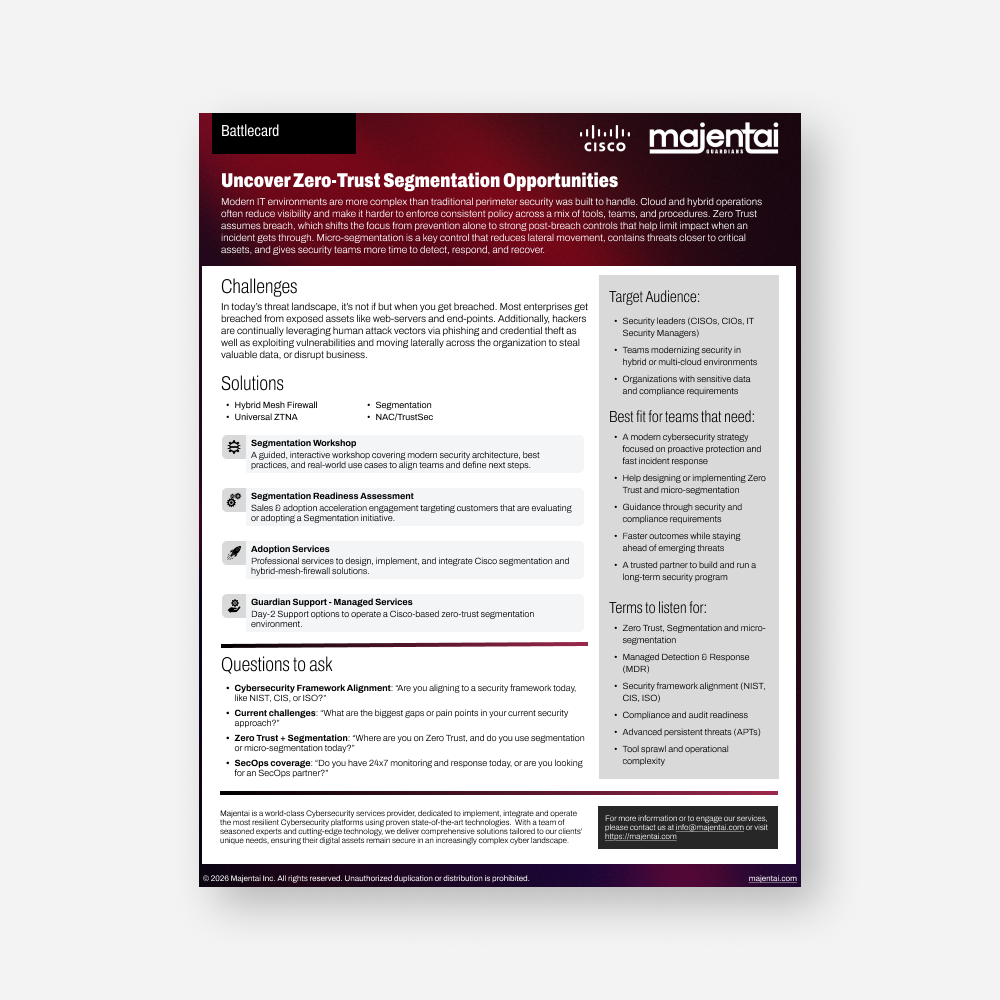
Uncover Zero-Trust Segmentation Opportunities
Modern IT environments are more complex than traditional perimeter security was built to handle. Cloud and hybrid operations often reduce visibility and make it harder to enforce consistent policy across a mix of tools, teams, and procedures. Zero Trust assumes breach, which shifts the focus from prevention alone to strong post-breach controls that help limit impact when an incident gets through. Micro-segmentation is a key control that reduces lateral movement, contains threats closer to critical assets, and gives security teams more time to detect, respond, and recover.