Win Wire: State Agency
A state transportation agency partners with Majentai to support its Mobile ID program by securing production environments and enhancing access controls. The engagement begins with a Cisco-funded workshop and Zero Trust strategy alignment, progressing into a custom, phased deployment of ISE, DUO, and Umbrella. Through advanced workshops and production system integration, the agency achieves policy modeling and enforcement across five environments—dramatically increasing visibility and reducing risk. The work also justifies additional Cisco technologies within their ELA.
Win Wire: Automation Software Provider

An automation software provider engages Majentai to implement Cisco Secure Workload following a successful proof of value. The engagement includes policy modeling for production systems, risk discovery, and access control refinement. In just four weeks, the provider achieves improved visibility, tighter enforcement posture, and operational efficiencies through automated controls and segmentation strategies. The work sets the foundation for scalable policy enforcement and long-term Zero Trust alignment.
Win Wire: Healthcare

A leading healthcare institution engages Trace3 and Majentai to lead a Segmentation Readiness Assessment focused on securing its research network environments. The project includes stakeholder interviews, analysis of current segmentation efforts, and definition of a high-level framework that aligns with HIPAA and other compliance mandates. Critical systems in scope include EHR platforms, research data, and specialized imaging devices. The outcome includes a clear segmentation strategy, supporting documentation, and a roadmap for phased implementation.
Segmentation Workshop
Understanding what exists is only the beginning. Controlling it is what builds resilience. Magentai’s Segmentation Workshop helps teams move from visibility to action using Zero Trust principles to protect critical assets without disrupting the business.
Integrated Cybersecurity Workshop

Magentai presents its modular Integrated Cybersecurity Workshop – a customizable engaging, interactive event focused on helping you dive into Secured hybrid- cloud architectures, essential services, design-patterns, and application evolution.
Customers will get an overview of current techniques and practices with comparisons to current methods, and tool-sets. This interactive workshop includes use cases, presentations, and demonstrations that will get you and your team quicklly up to speed on the latest in Modern Cybersecurity.
Zero Trust Security Posture Assessment

Magentai’s Zero Trust Security Posture Assessment evaluates your current security ecosystem to identify architectural gaps, assess tool effectiveness, and recommend a roadmap to achieving Zero Trust maturity. We analyze across identity, devices, networks, applications, and data to ensure every user, device, and access request is continuously validated and verified.
Company Overview

Magentai is your trusted partner in safeguarding digital assets. Our team is certified in the most rigorous industry standards, ensuring top-tier protection and compliance for your business.
Cisco ISE Readiness Assessment
The Majentai ISE Readiness Assessment is designed to provide an expert evaluation of your current ISE environment, aligning it with your use cases, existing infrastructure, and critical security policies. This assessment ensures that any gaps are accurately identified and offers specific, actionable recommendations to bring your ISE implementation to optimal functionality.
Company Overview for Cisco
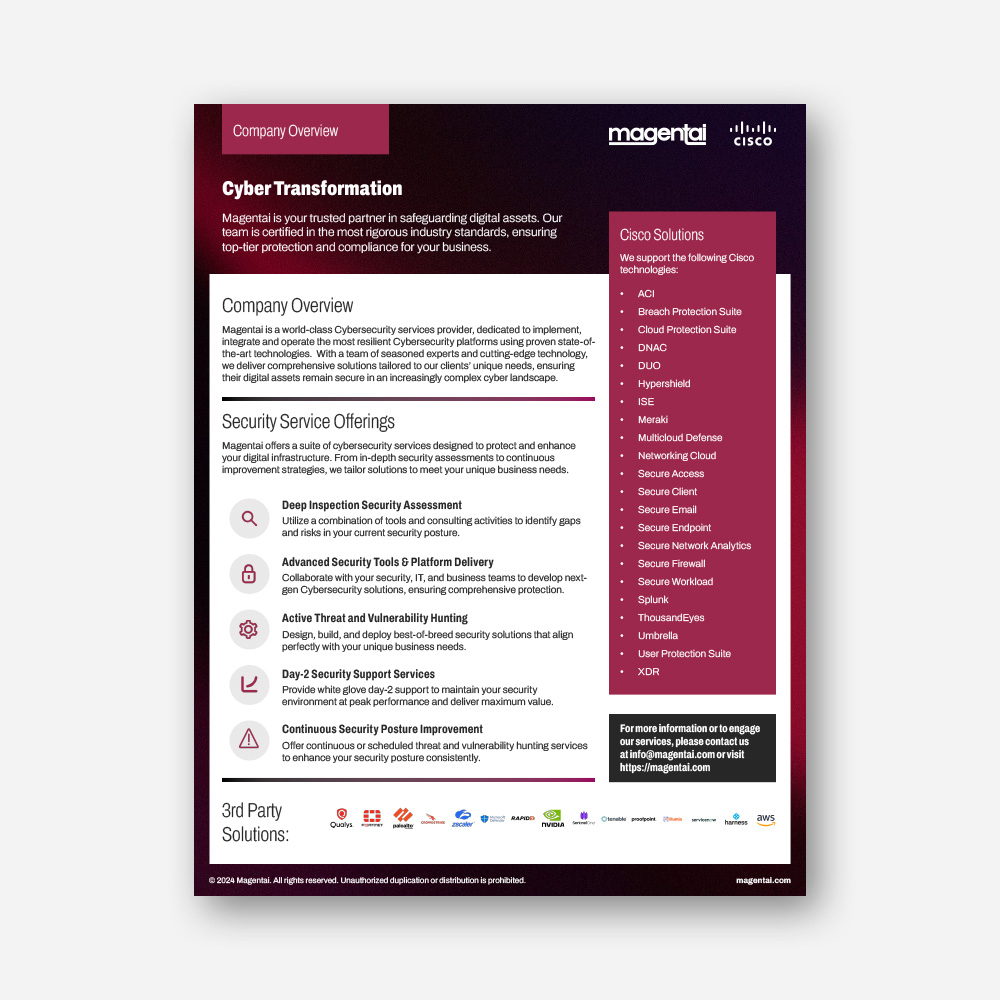
Magentai is your trusted partner in safeguarding digital assets. Our team is certified in the most rigorous industry standards, ensuring top-tier protection and compliance for your business.
Navigating Cybersecurity and AI Workshop

An interactive ILT session exploring how AI is transforming cybersecurity, moving beyond a buzzword to become a critical tool in combating sophisticated threats. We’ll cover key trends, real-world applications, and discuss both the benefits and challenges of integrating AI into cybersecurity strategies.