Cisco Identity Services Engine (ISE) Workshop
This Cisco Identity Services Engine (ISE) Workshop is a structured planning engagement designed to align business, IT, and OT stakeholders around a low-risk path to deployment. Majentai assesses current-state readiness, defines target-state architecture, and documents the phased roadmap, controls, and priorities needed to move toward implementation with greater confidence.
Cisco Secure Access (CSA) Workshop
This Cisco Secure Access (CSA) Workshop is a structured engagement designed to align business and technical stakeholders, validate current-state readiness, and define a phased deployment path for Secure Internet Access (SIA) and Secure Private Access (SPA). Majentai clarifies architecture, integrations, and governance needed to move to controlled enforcement.
Cisco Secure Workload (CSW) Workshop
This Cisco Secure Workload (CSW) Workshop is a structured engagement designed to align stakeholders, assess current-state realities, and define a phased deployment path with limited risk. Majentai documents architecture, telemetry, labeling, and operating model decisions needed to move from discovery toward controlled onboarding, validation, and enforcement readiness.
Cisco Secure Workload (CSW) Solution Overview
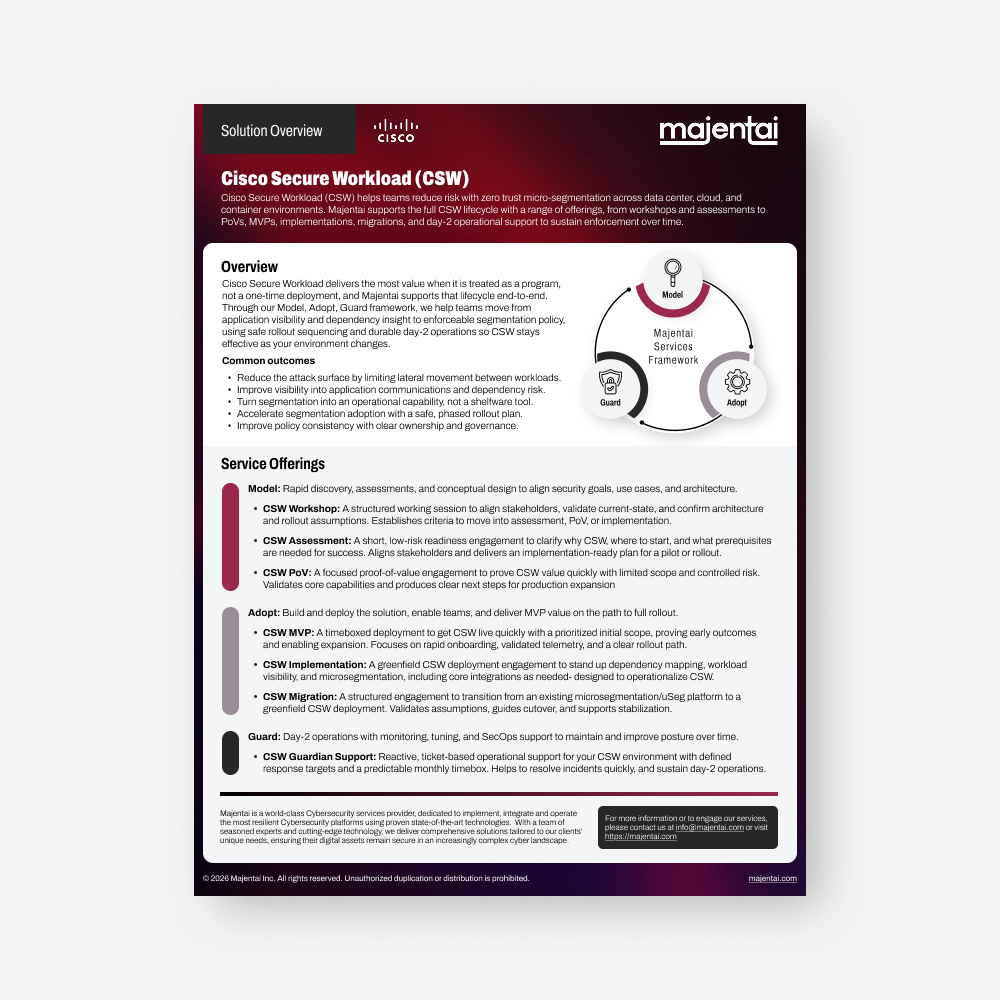
Cisco Secure Workload (CSW) helps teams reduce risk with zero trust micro-segmentation across data center, cloud, and container environments. Majentai supports the full CSW lifecycle with a range of offerings, from workshops and assessments to PoVs, MVPs, implementations, migrations, and day-2 operational support to sustain enforcement over time.
Segmentation Workshop
Understanding what exists is only the beginning. Controlling it is what builds resilience. Magentai’s Segmentation Workshop helps teams move from visibility to action using Zero Trust principles to protect critical assets without disrupting the business.
Navigating Cybersecurity and AI Workshop

An interactive ILT session exploring how AI is transforming cybersecurity, moving beyond a buzzword to become a critical tool in combating sophisticated threats. We’ll cover key trends, real-world applications, and discuss both the benefits and challenges of integrating AI into cybersecurity strategies.